Technology and data is the core of most organizations. But what is cyber security and have you put the effort into effective cyber security? We’re here to explain what it is and cyber security practices for effectively defending against hazards in the digital world with the help of Mike at Cybir!
Cybir is a continued core focus on a full suite of in-house cyber security, digital forensics, and data recovery expertise, honed for litigation support, eDiscovery, and expert witness services.

What Is Cyber Security?
Cyber security (as stated by Merriam-Webster ), is the measures taken to protect a computer or computer system against unauthorized access or attack.
Any organization that uses modern technology must face with the risk of cyber threats. Taking steps to address this risk is crucial for the operational security of businesses. Data breaches and cyber-attacks against businesses have the potential to cause huge financial and reputational damage. It could not only affect the business, but also the employees.
Examples of Cyber Threats
Malware
 Malware, shorthand for “malicious software,” is an application that’s intended to cause damage to systems, steal data, gain unauthorized access to networks, or otherwise wreak havoc. This is the most common type of cyber threat.
Malware, shorthand for “malicious software,” is an application that’s intended to cause damage to systems, steal data, gain unauthorized access to networks, or otherwise wreak havoc. This is the most common type of cyber threat.
There are a number of malicious software variants, including:
- Viruses – Attaches themselves to clean files, replicate, and spread to other files. They may delete files, force reboots, join machines to a botnet, or enable remote backdoor access to infected systems.
- Worms – Similar to viruses, but without the need for a host file. Worms infect systems directly and reside in memory, where they self-replicate and spread to other systems on the network.
- Backdoor – Used by attackers to secure remote access to infected systems, or to obtain unauthorized access to privileged information.
- Trojans – Disguises themselves as a legitimate application, or simply hide within one. They discretely open backdoors to give attackers easy access to infected systems, often enabling the loading of other malware.
Ransomware
 Ransomware is a type of malicious software that infects a computer and restricts users’ access to it until a ransom is paid to unlock it. Ransomware attacks often rely on social engineering techniques such as phishing, tricking users into downloading a dropper that retrieves and installs the payload. Once on the system, ransomware finds all files of a specific type locally and across the network, encrypting and often stealing them. The original files, recovery points, and backups are then deleted to prevent users from restoring the system on their own. Ransomware usually changes the file extension and adds a “help” file, explaining how victims can pay to recover their data.
Ransomware is a type of malicious software that infects a computer and restricts users’ access to it until a ransom is paid to unlock it. Ransomware attacks often rely on social engineering techniques such as phishing, tricking users into downloading a dropper that retrieves and installs the payload. Once on the system, ransomware finds all files of a specific type locally and across the network, encrypting and often stealing them. The original files, recovery points, and backups are then deleted to prevent users from restoring the system on their own. Ransomware usually changes the file extension and adds a “help” file, explaining how victims can pay to recover their data.
Mike at Cybir also mentions data exfiltration. He states, “Ransomware is evolving where threat actors are also stealing data and saying, ‘ok great your backups worked and you restored, but you are still going to want to pay us if you do not want us to leak your data to the internet or dark web.'”
He states for protection, “For ransomware and malware traditional AV is no longer effective. Traditional AV basically has a definitions file where when it is running a scan it looks at the current file and compares it to its list of known good/bad files and then makes a decision about what happens to it from there. If it does not know anything about the file it likely skips right over it and allows it to pass. EDR/MDR/XDR SentinelOne provides best-in-class NextGen Antivirus, device control, firewall control, and threat hunting capabilities.”
Cybir offers endpoint protection, detection, and response in conjunction with SentinelOne which provides best-in-class NextGen Antivirus, device control, firewall control, and threat-hunting capabilities.
Phishing
Phishing is a common attack technique that manipulates people into taking unsafe actions or divulging sensitive information. In typical phishing campaigns, attacks will use different types of communication – email, instant messages, SMS, and websites – to impersonate a trustworthy person or organization that they are familiar with and use that identity to trick users into clicking on malicious links, downloading malware-laden attachments, or disclosing sensitive personal information.
Mike at Cybir states, “This often leads to ransomware or a business email compromise type of attack.”
One way to stay protected from phishing attacks is through training and education. Mike at Cybir states, “The keys are constant user training and education as well as a solution like iron scales that are going to profile an email and add banners/details to give the user a heads up.”
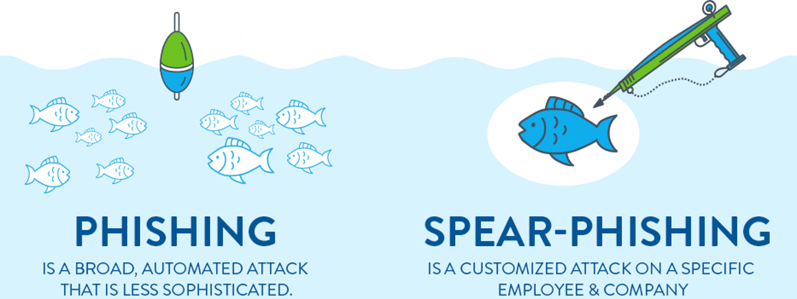
There are two types of phishing attacks – phishing which is wide-ranged and spear phishing which is targeting a specific individual/company.
Spear phishing requires a lot of research for the attacker, but these cyber threats are generally tailored to their target based on insider knowledge or information available on the web and/or through social media. They use reputable names within the company to attack someone who they think will fall for it. It requires extra effort to spear phish, but they are more likely to succeed.
PCS offers a variety of phishing training products to help you and your company stay protected and aware of what to look for when it comes to phishing attacks.
Knowing the different malicious attacks out there, there are ways to monitor and keep protected again malicious attacks.
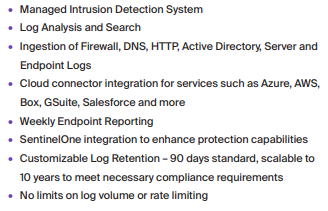
Cybir offers Security Operations Center As A Service (SOCAAS) with these key features –
Click here to learn more about PCS.
